Cellular community hacking refers to any unauthorized entry to your cell gadget or its communications. This will vary from high-level safety breaches to easy interception of knowledge over unsecured web connections. It will probably additionally embrace bodily theft of your telephone and subsequent hacking makes an attempt utilizing brute drive strategies.
Cybercriminals create many digital cell hacking instruments designed to insert dangerous packages and undesirable purposes into your cell gadget. They’ll extract delicate consumer inputs and confidential information from a compromised gadget or community. A few of these cell hacking instruments even enable the attacker to manage your gadget with out your permission.
Featured Companions: Community Monitoring Software program
How cell community hacking works
Attackers might use a wide range of ways to hold out a cellular phone community hack, however the course of usually includes figuring out the goal, discovering vulnerabilities, delivering malicious payload, exploitation, exfiltrating information, and overlaying tracks.

1. Figuring out the goal
Hackers typically select particular targets primarily based on a number of elements, similar to the worth of the knowledge saved on the gadget, the consumer’s profile, or potential monetary profit. Targets might be anybody; cyber criminals typically decide targets primarily based on what they’ll acquire, weighing elements similar to problem, danger, and potential take.
2. Discovering vulnerabilities
Attackers seek for weak spots in your gadget, working system (OS), or put in purposes. These vulnerabilities may additionally embrace outdated software program or easy-to-guess passwords.
3. Delivering malicious payload
Upon discovering vulnerabilities in your telephone, hackers deploy a malicious payload. This payload is a dangerous part like a virus or spy ware that may attain your cell gadget by means of totally different strategies, together with hackers sending a phishing e-mail, making a faux Wi-Fi hotspot, or embedding the payload inside an app.
4. Exploitation
After executing the malicious payload, hackers can exploit vulnerabilities to ascertain a foothold. These vulnerabilities might be weaknesses within the OS, outdated software program, or flaws in particular apps.
5. Exfiltrating information
As soon as entry is established, attackers might steal or exfiltrate delicate information and even take full management of your gadget. This will result in id theft, monetary fraud, or different malicious actions.
6. Masking tracks
Cybercriminals purpose to remain undetected for so long as doable to maximise the injury they’ll trigger and keep away from seize. They typically attempt to manipulate any proof of their intrusion by deleting log recordsdata, altering timestamps, or modifying different information that might expose their actions.
Furthermore, they might set up backdoors to bypass regular authentication procedures and entry a pc or community remotely with out detection. Some attackers additionally use refined strategies, particularly encrypting malicious code, exploiting zero-day vulnerabilities, or utilizing rootkits to keep away from detection as they execute assaults.
9 frequent methods hackers assault on cell
Cybercriminals use a number of strategies to conduct community hacking on cell units, like malicious apps, social engineering, phishing assaults, unsecured Wi-Fi networks, outdated software program, SMS-based assaults, Bluetooth exploitation, weak passwords, and {hardware} exploitation.
Malicious apps
Malicious apps are software program packages designed to compromise the safety of a cell gadget. They typically seem official however comprise dangerous parts similar to malware, spy ware, or ransomware, aiming to steal delicate info or management the gadget.
Social engineering
Social engineering includes manipulating people into divulging confidential info or performing actions that will compromise safety. Attackers exploit human psychology by means of strategies like impersonation, deception, or making a false sense of urgency.
Phishing assaults
Phishing assaults, essentially the most prevalent type of social engineering, contain misleading ways to trick customers into giving out login credentials or private information. Attackers typically use faux web sites, emails, or messages that mimic trusted sources to use consumer belief.
Unsecured Wi-Fi networks
Connecting to unsecured Wi-Fi networks exposes cell units to potential assaults. Hackers can exploit vulnerabilities in these networks to intercept information, launch man-in-the-middle (MITM) assaults, or distribute malware.
Outdated software program
Attackers goal identified weaknesses in outdated software program purposes or OS to realize unauthorized entry, set up malware, or conduct different malicious actions.
SMS-based assaults
SMS-based assaults contain the manipulation of textual content messages to deceive customers or benefit from vulnerabilities in messaging methods. These assaults might embrace phishing makes an attempt, malware distribution, or unauthorized entry by means of SMS channels.
Bluetooth exploitation
This happens when attackers leverage vulnerabilities in a tool’s Bluetooth performance to illegally entry, distribute malware, or intercept information exchanged between units.
Weak passwords
Guessable passwords make it simpler for attackers to get unlawful entry to cell units or accounts. Utilizing weak passwords or reusing them throughout a number of accounts will increase the danger of unauthorized entry and potential information breaches.
{Hardware} exploitation
Whereas software program safety is essential for cell community safety, it’s equally important to deal with {hardware} vulnerabilities that may undermine cell community safety. Attackers might exploit weaknesses in your gadget’s {hardware} elements, similar to baseband processors, SIM playing cards, Bluetooth, and Wi-Fi.
Methods to detect in case your cell gadget is hacked
There are indicators you possibly can look out for to detect cell gadget hacking, together with uncommon battery drain, sluggish efficiency, extreme information utilization, unfamiliar apps or frequent pop-ups, unusual texts or calls, overheating, suspicious account exercise, surprising permissions, gadget habits anomalies, and community irregularities.
- Uncommon battery drain: Your gadget’s battery is depleting quickly, even with minimal utilization. This might point out that malicious processes are operating within the background, consuming additional energy.
- Gradual efficiency: Your gadget experiences sluggish response instances, frequent delays, or crashes. This can be a results of hacking actions straining your gadget’s sources.
- Extreme information utilization: You discover a sudden and unexplained enhance in information consumption. This might be an indication that malware or hacking instruments are utilizing your information to speak with exterior servers.
- Unfamiliar apps or frequent pop-ups: New and unfamiliar apps seem in your gadget with out your consent, otherwise you observe frequent pop-ups. Malicious software program might set up extra apps or generate undesirable ads.
- Overheating: Your gadget turns into unusually sizzling, even throughout gentle utilization. This will point out that malicious processes are straining your gadget’s {hardware}, inflicting it to overheat.
- Suspicious account exercise: You detect uncommon exercise, unrecognized logins, or unauthorized entry in your accounts. Hackers might get into your accounts by means of compromised units.
- Surprising permissions: Apps request permissions that appear pointless for his or her declared perform. Malicious apps might search extra permissions to entry delicate information.
- Machine habits anomalies: Your gadget behaves unexpectedly, similar to turning on or off with out enter. Hacking actions could cause disruptions in regular gadget habits.
- Community irregularities: You observe community habits irregularities, like frequent disconnections or unfamiliar units related to your Wi-Fi. Hacked units might present irregularities in community connections.
Cellular community hacking prevention suggestions
Whereas a cell community may be hacked, there are various methods you possibly can forestall it. Utilizing robust passwords, updating software program repeatedly, enabling two-factor authentication (2FA) or multi-factor authentication (MFA), avoiding public Wi-Fi utilization, utilizing HTTPS, being cautious with app permissions, securing your Bluetooth, and putting in cell safety apps are among the methods you possibly can defend your gadget from community hacking.
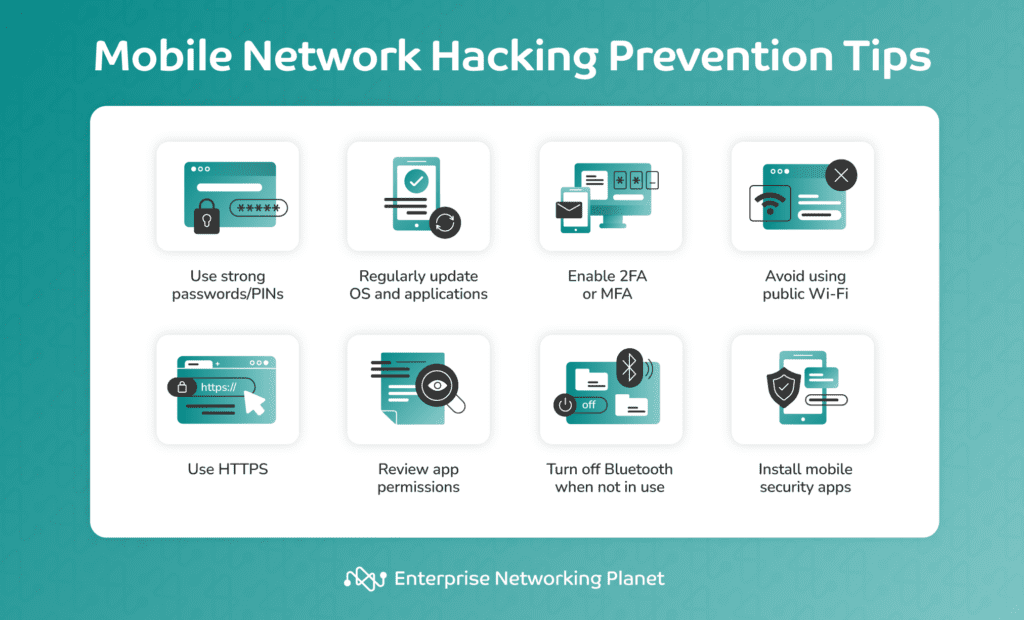
- Use robust passwords/PINs: Set robust and distinctive passwords or PINs to your cell gadget and SIM card. Keep away from utilizing “1234,” “password,” or different simply guessable passwords.
- Repeatedly replace software program: Hold your cell gadget’s OS and all put in apps updated to patch vulnerabilities and enhance safety. One of many easiest steps you possibly can take is to activate automated updates for each your apps and OS to boost safety.
- Allow 2FA or MFA: At any time when doable, allow 2FA or MFA to your cell accounts. This provides an additional layer of safety other than merely asking for a password by requiring extra types of verification, similar to a code despatched to your telephone or fingerprints.
- Keep away from utilizing public Wi-Fi: Connecting to a public Wi-Fi exposes your private information to anybody else utilizing the community. Keep away from utilizing public Wi-Fi for delicate actions or think about using a cell digital non-public community (VPN) to encrypt your web connection on public Wi-Fi networks.
- Use HTTPS: When looking web sites or utilizing apps, guarantee that you’re utilizing safe, encrypted connections (HTTPS). This helps defend information in your cell community from hacker interception.
- Be cautious with app permissions: Assessment and perceive the permissions requested by cell apps earlier than putting in them. Solely grant permissions which are obligatory for the app’s performance. Restrict the entry to different info in your gadget, together with your location, contacts, and pictures.
- Safe your Bluetooth: Disable Bluetooth when not in use, and ensure that your gadget isn’t set to be discoverable by different units. This prevents unauthorized entry or pairing.
- Set up a cell safety app: Think about using respected cell safety apps with antivirus safety, anti-malware scans, and app permission monitoring to assist defend your gadget from malicious software program.
Are 5G or 4G networks more durable to hack?
Each 4G and 5G networks have security measures designed to guard towards several types of community safety threats. Nevertheless, 5G networks are usually considered more secure than their predecessors as a result of a number of enhancements of their design.
Here’s a desk evaluating the security measures of 4G networks and 5G networks:
| Safety function | 4G | 5G |
|---|---|---|
| Encryption | Makes use of AES-128 for information encryption. | Makes use of the extra strong AES-256 encryption commonplace, considerably strengthening transmitted information safety. |
| Authentication | Depends on IMSI for consumer authentication. | Introduces 5G AKA, a complicated authentication technique that optimizes the safety of consumer id verification, decreasing the danger of unauthorized entry. |
| Community slicing | Restricted functionality for community slicing. | Implements superior community slicing, permitting the creation of remoted networks to forestall lateral motion. This makes it more durable for attackers to maneuver laterally as soon as they acquire entry. |
| Low-latency safety | Greater latency might influence real-time safety. | Low-latency design improves total community efficiency and the effectiveness of real-time safety purposes. This ensures immediate responses to safety threats. |
| Edge computing safety | Restricted help for safe edge computing. | Incorporates stronger safety measures for edge computing for the integrity and confidentiality of processed information on the fringe of the community to keep up the safety of decentralized computing environments (together with cell). |
Whereas 5G networks provide higher security measures, it’s necessary to notice that no community may be thought of fully hack-proof. Safety is an ongoing concern, and as expertise advances, so do the ways of cyberattackers.
Backside line: Cellular community hacking
Be cautious of the strategies hackers use to entry cell units, from faux web sites on phishing assaults to easy-to-guess passwords. Be careful for indicators that your gadget could also be compromised, like uncommon battery drainage, surprising information consumption, or unexplained community actions. Vigilance is essential, and it’s essential to concentrate on your gadget’s habits.
Common or automated updates and patches, utilizing cell VPNs, creating distinctive passwords, and proactive safety measures are important for sustaining a safe community setting. As well as, needless to say no expertise, be it 4G or 5G, can declare absolute invulnerability to cell community hacking, so at all times keep vigilance in your networks and units.
Reinforce your cell safety by safeguarding your enterprise cell apps. Learn our 5 Steps to Securing Your Enterprise Cellular Apps to search out out how one can defend what you are promoting information and purposes. Among the finest methods is utilizing a prime cell VPN to maintain prying eyes off your information.


